#Microservices #SoftwareArchitecture
For a long time, monolithic architectures ruled the roost when it came to application design. However, monolithic architectures can become difficult to manage and scale as applications grow and evolve over time. The idea of microservices emerged as a response to the limitations of traditional monolithic application architecture, which typically involves building an application as a single, large codebase with tightly-coupled components. By the mid-2000s, digital native companies such as Netflix, Amazon, and Twitter started experimenting with a more lightweight approach to building cloud-native applications and microservices , breaking them down into small, independent services. By 2025, ~75% of organizations report using microservices , with 23% more planning adoption soon. The idea was to build applications using the Unix philosophy of "Do one thing and do it well." The term "microservices" was coined in 2011 by James Lewis and Martin Fowler, two software architects who were advocating for this approach. Since then, microservices have become increasingly popular in software development, and many companies have adopted this architecture to build highly scalable, resilient, and flexible applications.
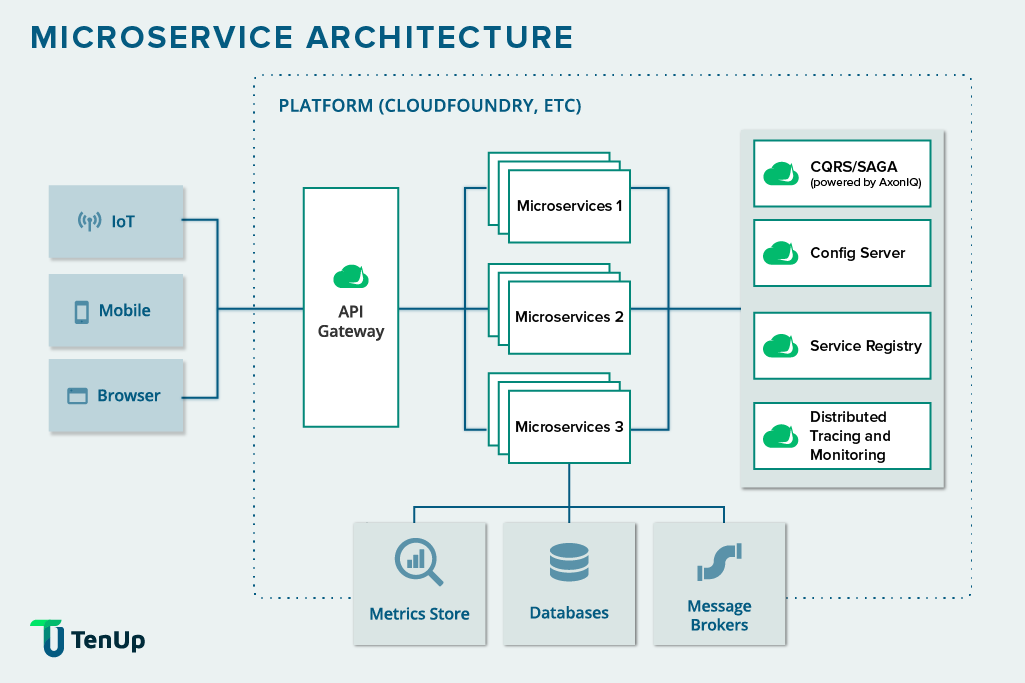
At its core, microservices architecture is a design approach for developing software applications as a collection of small, independent services. Each service is focused on a specific business capability and can be created, deployed, and scaled independently from other services in the application.
Consequently, each service typically has its own database and communicates with other services through lightweight APIs—an approach also widely used in Serverless architecture where functions interact via APIs. Developers can build and deploy each service independently, using the programming language and technology stack best suited to its needs. The global microservices architecture market is expected to grow from $6.27 B in 2024 to $15.97 B by 2029 at an 18.8% CAGR.
However, developing, deploying, and managing such a microservices architecture poses its own share of challenges. For instance, managing shared access, ensuring data consistency, maintaining the security of services, facilitating communication between services, and managing dependencies. To address these challenges, design patterns for microservices use architectural patterns that provide efficient administration of these services, overcome challenges, and maximize performance. By choosing the right microservices architecture patterns for your use case, you can increase component reusability and reduce development time and effort. Over time, this can eliminate the need to reinvent the wheel each time you make changes to your application.
While microservice architecture offers significant advantages like independent scalability, modularity, and faster release cycles, real-world implementations often expose underlying complexities that aren't obvious during the initial phases of microservices development.
As organizations begin building microservices or migrating from monoliths, they face architecture-level challenges:
These aren’t just edge cases—they’re everyday realities in microservices-based applications. That’s where microservices design patterns and architecture patterns come in. Organizations adopting microservices reported 63% faster deployment speed , 56% improved agility, and 51% better scalability.
That’s where microservices design patterns and architecture patterns come in.
These are system design patterns and best practices specifically tailored for distributed systems. They help teams streamline microservices implementation by solving critical concerns such as:
Without using design patterns for microservices, teams often reinvent solutions, introduce fragility, or face scalability bottlenecks.
By using the right microservices architecture patterns, teams can create a system that is:
Whether you're just starting your journey or planning a monolithic to microservices migration, understanding different design patterns—and the evolution from monolithic to microservices architecture —is key to long-term success.
While there are several microservices design patterns, we'll discuss some of the most noteworthy and commonly used design patterns here. Find out why they are important and how they are used.
As a microservices-based application grows in complexity, the number of endpoints can become unwieldy—just one of the challenges developers face when building scalable cloud-based apps. An API gateway acts as a single entry point to the application, abstracting away the complexity of the underlying microservices.
Why It’s Useful:
Key Functions:
Additional Benefits:
Modern microservices architectures often adopt token-based authentication standards like OAuth2 and OpenID Connect to secure user access and assign permissions. This approach ensures that every request is verified and authorized before it reaches the intended service.
Use Case Example:
A SaaS platform issues JWT (JSON Web Token) access tokens to authenticated users and validates scopes or claims on each microservice request, ensuring that users only access resources they are permitted to.
Best Practices:
API gateways also provide other important functions, such as authentication, rate limiting, request/response transformation, and service discovery. These features can help improve the security, scalability, and reliability of a microservices architecture.
Another benefit of using an API gateway is that it can simplify the management and monitoring of a microservices architecture. By centralizing the routing and communication between services, an API gateway can provide a single point of control for managing traffic and monitoring service performance.
Access tokens are commonly used as a security mechanism in microservice architecture to authorize and authenticate requests between services.
How it works:
Token Management:
Why It Matters:
For sensitive workloads, mutual TLS provides an additional layer of security by requiring both the client and the server to present valid certificates during the connection handshake. This ensures encrypted communication and mutual trust between internal services.
Use Case Example:
In a financial services application, all internal API calls are encrypted using mTLS to safeguard transactions and protect customer data in transit.
Why It’s Critical:
Access tokens are typically generated by an authentication service or identity provider, which is responsible for verifying the identity of users or services and issuing access tokens. The access token usually contains information about the user or service that it represents, as well as a time-to-live (TTL) value that indicates how long the token is valid.
In addition, to the security benefit, access tokens allow for improved scalability and flexibility in a distributed architecture.
Service discovery is the automatic detection of devices and services over a network, reducing manual configuration efforts in microservices and containerized environments, often supported by a service mesh for secure microservice communication.
Why It’s Important:
How It Works:
Popular Tools:
Benefits:
There are different ways to implement service discovery in microservices, but one common approach is to use a service registry. A service registry is a central repository that keeps track of all the services in the system, along with their location and other relevant metadata. When a service needs to communicate with another service, it queries the service registry to find the location of the desired service, and then establishes a connection to it.
Some popular tools for implementing service discovery and service registries in microservices include Consul, etcd, and ZooKeeper. Additionally, some container orchestration platforms, such as Kubernetes, have built-in support for service discovery.
Secure Service Discovery
While service discovery ensures connectivity, securing it is crucial to prevent spoofing or unauthorized service registration.
Use Case Example:
Microservices register themselves with a secure registry such as Consul or Eureka, which validates the identity of each service before accepting registration.
Security Tips:
The circuit breaker pattern improves the resilience and fault tolerance of microservices by detecting failures and temporarily halting access to affected services.
How It Works:
Why It’s Needed in Microservices:
Benefits:
Distributed tracing provides visibility into the flow of requests between microservices, helping diagnose bottlenecks and errors.
How It Works:
Core Components:
Benefits:
CQRS and Saga patterns enhance scalability, performance, and transaction management in distributed systems.
CQRS (Command Query Responsibility Segregation):
Saga Pattern:
Benefits:
Please read our blog on the importance of CQRS and SAGA in microservices architecture to better understand these microservices design patterns.
Zero Trust Security Model
Zero Trust assumes no service or user is trusted by default, even inside the private network. Every request must be verified and authorized.
Best Practices:
Why It Matters:
Zero Trust reduces the attack surface and improves compliance, which is increasingly critical in the era of cloud-native microservices vs. cloud-based monoliths.
To break down the architecture into microservices , organizations must apply strategic decomposition patterns to ensure maintainability and scalability.
Key Types:
Use Case Example:
An eCommerce platform splits into User, Cart, Checkout, and Recommendation services, each developed and deployed independently.
Each microservice manages its own database, ensuring loose coupling and autonomy.
Use Case Example:
A logistics platform uses separate databases for Shipment, Tracking, and Notification services.
Benefits:
Microservices architecture offers a number of benefits for modern application development. However, to leverage its full potential, developers need to identify and deploy relevant design patterns. By using the patterns listed here and others, developers can create microservices-based applications that are easier to develop, maintain, and scale.
Our developers have experience creating microservices architecture for a variety of applications across industries. Please read our case study titled Future-Proofing an Established Marine ERP through Microservice Architecture. We utilize different microservices design patterns to develop highly scalable, flexible, and resilient applications in both Cloud and Non-Cloud (On-premise and Hybrid) environments. Need accelerated development and streamlined maintenance with microservices architecture? Our specialized Product Engineering and Cloud Solutions can help!
Use the Strangler Fig pattern to replace monolith features step-by-step with microservices behind an API gateway. Combine it with Decomposition by subdomain, Service Discovery, Circuit Breaker, and Saga for smooth migration, fault tolerance, and data consistency.
Start with business capabilities—each service should map to a distinct domain function. Aim for high cohesion within services and loose coupling between them. Consider team ownership, fault tolerance, and deployment independence. Avoid overly fine-grained “nano-services” that increase complexity without real benefits. Evolve service boundaries as your system grows.
Yes, and it’s often essential. Combining microservices patterns—like API Gateway with Circuit Breaker or CQRS with Event Sourcing—helps solve complex, real-world problems efficiently. The key is balance: use patterns that complement each other, avoid over-engineering, and ensure maintainability.
Event Sourcing captures every change as an event, enabling full audit trails, rollback, and reliable CQRS projections. It’s ideal for domains needing traceability, like finance or logistics.
Smells like shared databases, synchronous coupling across services, excessive synchronous chatty RPC, god‑services, and improper transaction management (e.g. two‑phase commit) are frequently cited anti‑patterns on Reddit and SO communities.
Microservices security focuses on zero-trust architectures with service meshes, pod-level mTLS, fine-grained RBAC via identity providers, API gateway enforcement, and secure service discovery with identity validation, enhancing resilience, traceability, and defense-in-depth.
In modern microservices QA, you measure resilience (error rate, recovery time), scalability (throughput, latency under load), coupling (service blast radius), and developer velocity. Use metrics as fitness functions to validate whether a pattern (e.g. Circuit Breaker, Bulkhead) improves overall quality or not.